Identity Threat Detection (ITDR)
Detect identity-based threats targeting both human users and non-human identities — compromised service accounts, abused API keys, hijacked OAuth tokens — across SaaS and cloud.
MITRE ATT&CK-aligned detections. Real-time response. No alert noise.
Modern Attacks Don’t Look Like Attacks
Today’s attackers rarely rely on malware or exploits. They use valid credentials, legitimate access paths, and trusted integrations to move silently through environments.
Without identity context, these attacks remain invisible until damage is done.
The Verizon DBIR 2024 confirms it: attackers don't hack their way in anymore — they log in. Using compromised credentials, abused OAuth tokens, and over-privileged service accounts, they move silently through environments until damage is done.
“28% of incidents in French enterprises in 2025 were caused by account and permission management failures — not external attacks, but access that should have been revoked.” — CESIN Barometer 2026
Traditional security tools struggle to detect:
- Credential stuffing & brute force attempts
- MFA fatigue & push bombing attacks
- Privilege escalation using legitimate permissions
- Abuse of service accounts and machine identities
- SaaS and cloud access outside of expected behavior
Identity-First Threat Detection
Cydenti takes a fundamentally different approach to threat detection by focusing on identity behavior and access relationships — not just events or alerts.
"By correlating activity across identities, permissions, resources, and integrations, Cydenti reveals how access is being used, not just that it occurred."
Continuous Identity Behavior Analysis
Behavioral Anomalies
Detects deviations from normal access patterns across users, service accounts, and applications.
Credential Misuse
Identifies abnormal login activity, suspicious session behavior, and misuse of valid credentials.
Privilege Escalation
Flags attempts to gain higher privileges through role changes, permission abuse, or risky access paths.
Machine Identity Abuse
Monitors non-human identities for excessive access, unusual activity, and unauthorized usage.
Risky Authentication Flows
Detects insecure or abnormal authentication methods across SaaS and cloud environments.
How Cydenti Detects Identity Threats
Build Identity Context
Cydenti continuously maps identities, permissions, roles, and access paths using the Identity Graph.
Establish Behavioral Baselines
AI models learn normal behavior across identities and environments.
Detect Anomalies & Abuse
Cydenti identifies deviations that indicate compromise, misuse, or escalation.
Prioritize by Risk & Impact
Threats are scored based on exposure, blast radius, and downstream access.
Recommend Action
Cydenti provides clear remediation guidance aligned to security workflows.
Clear, Actionable Detection — Not Alert Noise
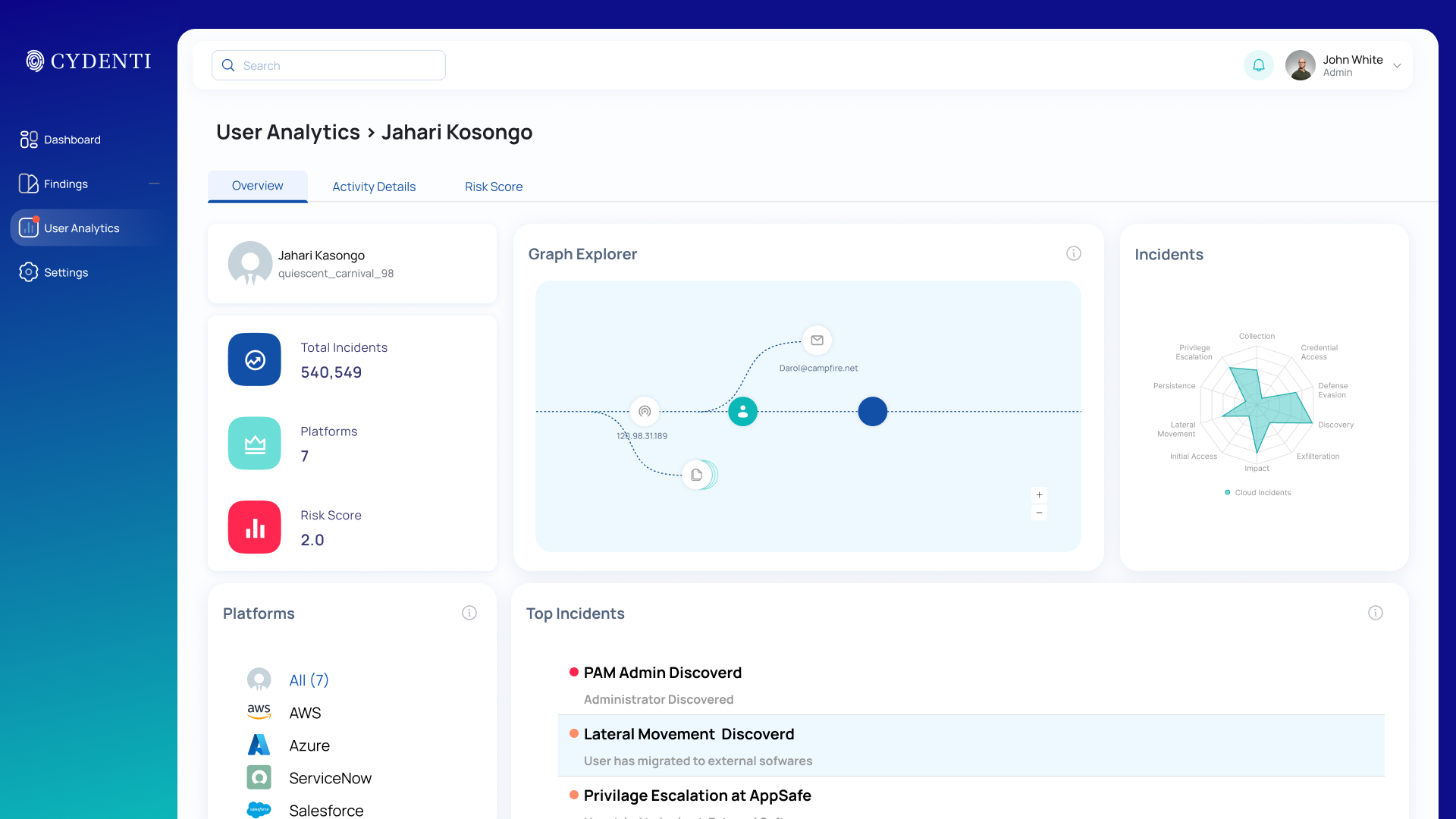
In the Cydenti Platform, You See:
- Identity-centric threat timelines
- High-risk identity and account rankings
- Contextual access paths showing impact
- Machine identity and service account risk views
- Recommended remediation actions
Security Outcomes That Matter
Early Threat Detection
Detect identity-based attacks before data exfiltration or system compromise.
Reduced MTTR
Understand who is impacted, what is exposed, and how to fix it — instantly.
Complete Coverage
Secure humans, machines, and AI agents with the same detection logic. Aligned to MITRE ATT&CK — your team already knows the framework.
Fewer False Positives
Contextual analysis dramatically reduces alert fatigue.
Works With Your Existing Stack
Cydenti doesn't just detect threats—it triggers automated responses through your existing SIEM and SOAR tools.
SIEM Integration
Send high-fidelity alerts to Splunk, Datadog, or Microsoft Sentinel for centralized monitoring.
SOAR Automation
Trigger automated playbooks in Tines, Torq, or Cortex XSOAR to contain threats instantly.
Ticketing & Chat
Push notifications to Slack, Teams, or Jira for immediate visibility and tracking.
Identity Threat Detection is powered by:
This ensures detection is not isolated — it drives real security outcomes.
Built for Identity-Centric Security Teams
Cydenti helps teams detect identity threats without rebuilding their entire security stack.
“Without Cydenti, a ghost service account would have remained active with access to 3 years of R&D data. Detected on the very first audit.”
— IT Director, Industrial SMB (120 employees)
Découvrez vos angles morts en 48 heures
— gratuitement.
NIS2 entre en vigueur le 1er octobre 2026. L’Audit Flash vous donne un rapport complet sur votre posture identitaire — comptes de service, comptes orphelins, exposition OAuth — en 27 minutes. Sans engagement.
Sans engagement · Données hébergées en France · Réponse sous 24h