Solutions de sécurité des identités pour
le SaaS et le Cloud
La plateforme souveraine européenne pour la sécurité des identités SaaS. Protégez chaque identité, humaine comme machine, dans vos environnements SaaS et cloud. Bloquez les menaces identitaires, encadrez l'usage de l'IA et prouvez votre conformité, sans recruter une nouvelle équipe ni remplacer vos outils existants.
Why Traditional Security Fails
Security teams are struggling to keep up with the speed of SaaS adoption and cloud complexity.
Fragmented Visibility
Siloed views across SaaS and cloud environments leave security teams in the dark.
Ghost Accounts
A former employee still has access to your Salesforce CRM. An intern inherited admin rights. These zombie accounts exist in most organizations — silently.
Manual Audits
Spreadsheets and screenshots can't keep up with the speed of modern development.
Shadow Connections
Your SaaS tools interconnect via APIs and OAuth tokens. Salesforce talks to Slack, which talks to GitHub. Every connection is a potential attack surface — and most are invisible.
Non-Human Identity Risk
For every employee, there are dozens of non-human accounts: bots, API keys, AI agents, automation scripts. They have broad access, no owner, and are never reviewed. (OWASP NHI Top 10, 2025)
Compliance Gaps (NIS2, DORA, GDPR)
28% of security incidents in 2025 traced to account and permission management failures (CESIN 2026) — exactly what NIS2 Article 21 requires organizations to prevent. One-per-year audits don’t meet the standard.
How Cydenti Solves It
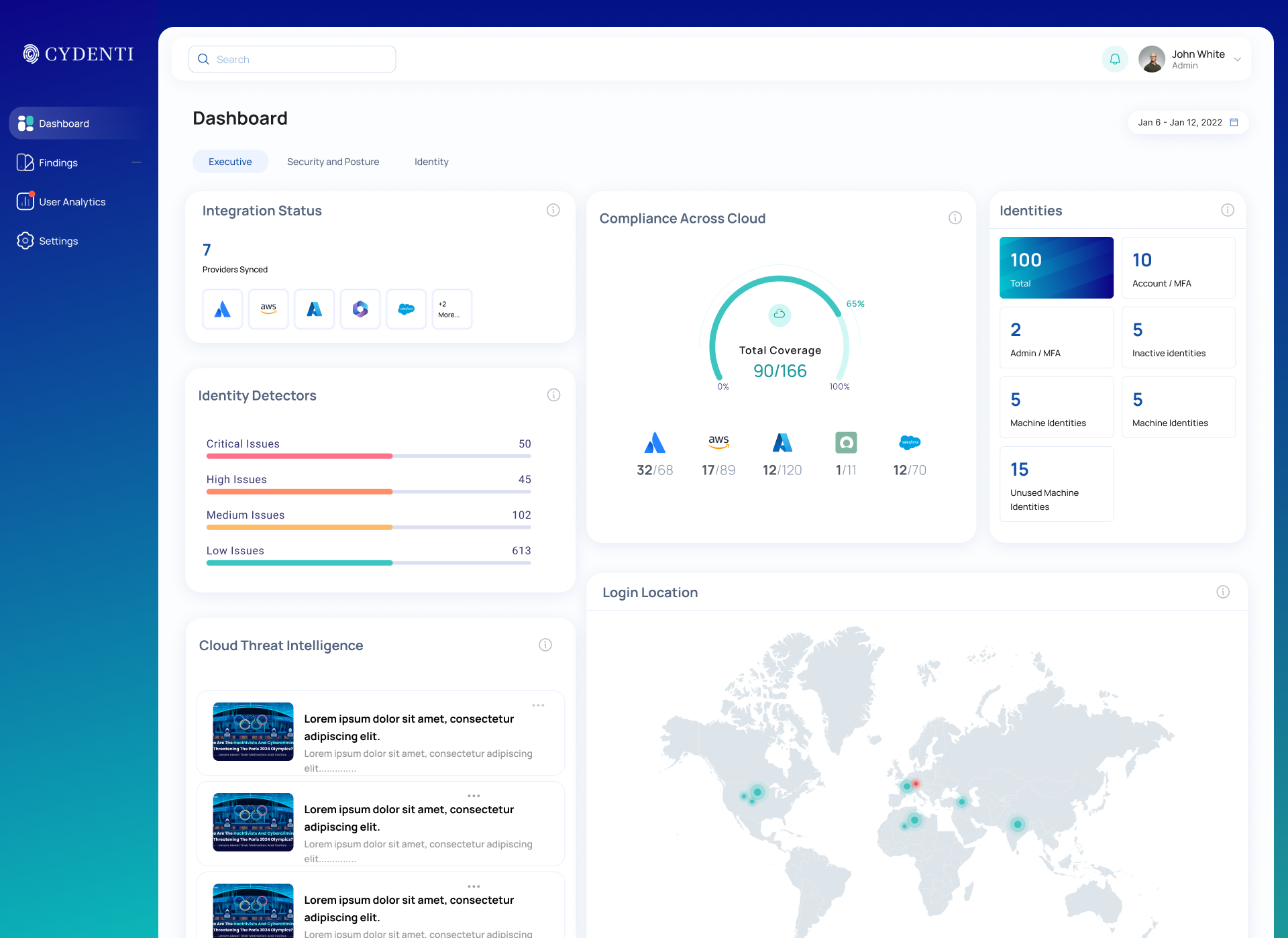
A complete platform to secure your identity perimeter from end to end.
Unified Visibility
Get a single pane of glass for all your identities across SaaS and cloud. Identify vulnerabilities, track user behavior, and visualize access paths in one intuitive dashboard.
Automated Governance
Automate access reviews and policy enforcement. Create custom workflows to certify access, revoke unused permissions, and ensure continuous compliance without the manual headache.
Threat Detection
Detect and respond to identity threats in real-time. Our AI analyzes behavioral signals to flag suspicious logins, privilege escalation, and shadow admin creation before damage occurs.
The Cydenti Advantage
Drive security outcomes that matter to your business.
360° Visibility
Identity, SaaS, cloud, and integration risks in one place.
Reduced Risk
Proactively identify and remediate vulnerabilities.
Audit Readiness
Always-on compliance monitoring.
Faster Response
Slash investigation time with context-rich alerts and automated workflows.
Empowering EveryStakeholder
From the CISO to the DevOps engineer — Cydenti gives every team the visibility and control they need, without adding complexity or requiring new headcount.
CISO / Security Leaders
Gain executive-level visibility across your entire identity attack surface — including the service accounts, API keys, and OAuth tokens that outnumber your workforce 45 to 1. Prove security ROI with quantifiable risk reduction and ensure resilience against identity-based attacks.
Strategic Value
- Unified visibility across SaaS, Cloud, and Identity
- Governance of non-human identities: service accounts, API keys, OAuth tokens
- Automated compliance reporting (ISO, SOC2, NIS2)
- Strategic risk prioritization based on business context
IAM & GRC Teams
Move beyond manual audits and spreadsheet tracking. Automate user access reviews, enforce least privilege, and maintain continuous compliance with evolving regulations.
Operational Efficiency
- Streamlined access certification campaigns
- Continuous monitoring for configuration drift
- Automated evidence collection for audits
SOC / Incident Response
Eliminate alert fatigue with identity-centric context. Quickly correlate disparate signals to identify compromised accounts — including hijacked service accounts and abused API keys — insider threats, and lateral movement before damage occurs.
Threat Context
- Rich identity context for every alert, human and non-human
- Detection of compromised service accounts and token abuse
- Faster mean-time-to-resolution (MTTR)
- Detection of anomalous behavior and impossible travel
IT & DevOps
Empower engineering teams to move fast without breaking security. Integrate identity security into CI/CD pipelines and automate routine access requests to reduce helpdesk friction.
Frictionless Security
- Self-service access with automated guardrails
- Visibility into machine identities and service accounts
- Seamless integration with existing workflows
Comprendre comment la solution fonctionne
Ces pages aident les acheteurs à comprendre comment la solution fonctionne, le rôle de chaque brique et la documentation disponible pour aller plus loin.
Comment l'Identity Graph cartographie les relations d'accès
Voir comment les identités, les permissions et les systèmes connectés s'articulent.
Pourquoi l'AI Risk Engine priorise ce qui compte
Comprendre comment le risque est classé pour que les équipes se concentrent d'abord sur les bons sujets.
Ce que couvre l'ISPM dans la posture d'identité SaaS
Découvrir comment la plateforme surveille les contrôles d'identité et l'exposition.
Comment l'ITDR détecte et répond aux menaces d'identité
Explorer le flux de réponse derrière la détection des menaces fondées sur l'identité.
Guides de mise en œuvre et documentation produit
Aller plus loin sur le paramétrage, les workflows et les questions que les acheteurs posent souvent.
Identifiez vos angles morts en 48 heures
— gratuitement.
Commencez par un POC d'un mois sur vos vraies données. Connectez vos 3 principales applications SaaS. Recevez votre premier rapport de risque. Décidez ensuite, sans pression.
Sans engagement • Sans carte bancaire • Hébergé en Europe • Réponse sous 24h